Copying files between Linux systems is very common. In this article you will learn how to copy files in a secure way using the SCP command on Linux (and Unix-like systems).
What is the SCP Linux command?
The protocol used for copying files between computers is SCP (Secure Copy Protocol) that is based on the Secure Shell (SSH) protocol. The command you can use to transfer files via the SCP protocol is the scp command that allows to transfer files between your local machine and a remote host or between two remote hosts.
No matter if you are a support engineer, systems administrator or developer at some point, it’s likely that you will have to transfer files using SCP.
In this article we will look at the first scenario, the most common, copying files from your local machine to a remote host (aka remote system) and viceversa.
It’s easy to figure out the second scenario (copying files between two remote hosts) once you have the basic knowledge about how to use scp.
Let’s start!
SCP Linux Command to Transfer Files From Local Host to Remote Host
First of all, let’s have a look at the basic syntax of the scp command on Linux.
scp [-i identity_file] [-P port] source targetFor now let’s ignore the flags enclosed by square brackets considering that these are optional flags.
Any flags surrounded by square brackets in the help or manual of a Linux command are optional.
We will look at the scenario where source and target of the command can be either a:
- Path on your local host
- Path on a remote host in the form [user@]host:[path]
It’s time for an example…
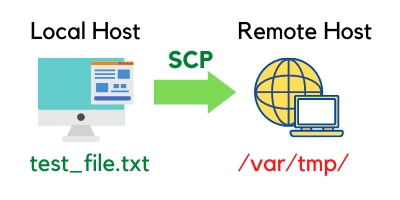
I want to do a secure copy of the file test_file.txt from the current directory on my local machine to the /var/tmp/ directory on a remote host with hostname test_host.
To copy the file to the remote system I will connect to it using the user test_user.
Here is the secure copy command…
scp test_file.txt test_user@test_host:/var/tmp/If we go back to the generic syntax we have seen before:
scp source target The value of source is test_file.txt.
The value of target is test_user@test_host:/var/tmp/ that matches the format we have mentioned before: user@host:path.
So, when we run this via the Linux command line, we see:
myuser@localhost:~$ scp test_file.txt test_user@test_host:/var/tmp/
Password:
test_file.txt 100% 5 0.5KB/s 00:00 As you can see from the Linux terminal scp asks for a password.
Which password?
The password to connect to the remote host test_host as the user test_user.
All good so far, let’s try something else…
Using the SCP Command Without Providing the Username
According to the expression [user@]host:[path] both user and path are optional (they are surrounded by square brackets) when we copy files using secure copy.
What happens if we remove the user part for the target from our command?
The target becomes host:path, let’s execute the command…
myuser@localhost:~$ scp test_file.txt test_host:/var/tmp/
Password:
Password:
Password:I’m using the same password I have used in the previous example. But for some reason it doesn’t seem to work…
The reason is very simple!
This time in the target we are not specifying the user. This means that the scp command automatically uses the local Linux user myuser to connect to the remote host.
This will only work if the user myuser also exists on the remote system. And this is not the case for the remote system I’m connecting to.
Also, even if the user myuser exists on the target system, myuser on the local and on the target system might have different passwords.
Using the SCP Command Without Target Path
If we remove the target path in the secure copy command, the target becomes user@host: …
myuser@localhost:~$ scp test_file.txt test_user@test_host:
Password:
test_file.txt 100% 5 0.5KB/s 00:00 This time the command works because we are connecting to the remote host as test_user.
But, where is the file being copied considering that we haven’t provided a path in the target?
The path is set by default to the home directory of the user we are connecting as to the remote host, the user test_user.
The default home directory on a Linux system for the test_user is /home/test_user/. But it can also be configured to a different directory.
And what if…
…you want to copy a file from the remote host to your local machine?
SCP Linux Command to Transfer Files From Remote Host to Local Host
The syntax for the scp command still applies. The only difference is that we swap source and target compared to the previous command.
The source is the remote host and the target is the local host.
Let’s copy the file remote_file.txt located in the directory /var/tmp/ on the remote host to the current directory on our local machine:
myuser@localhost:~$ scp test_user@test_host:/var/tmp/remote_file.txt .
Password:
test_file.txt 100% 5 0.5KB/s 00:00 There are two differences compared to the previous command:
- In the source part of the command (the file on the remote host) we specify the full path of the file we want to copy.
- The target is simply . (a dot) that represents the local directory. It could be any directory on our local machine. The . is a relative path from our current directory. To refer to file names when doing a secure copy we can also use an absolute path by specifying the full path of the directory on our system.
The password we provide when executing the command is still the password for test_user on the remote host test_host .
That’s because we are connecting to it to copy the file from it to our local computer.
I know it might not be easy understanding this command the first time you see it.
So take your time, and try to execute it on your computer.
Other Command Line Options For SCP
The generic syntax I have showed you at the beginning of this article was the following:
scp [-i identity_file] [-P port] source targetWe haven’t seen yet how the optional flags -i and -P can be used.
It’s very common having to use them, that’s why I want to briefly talk about them:
- -i identity_file: used to select the private key for public key authentication. It’s a way to connect to a target host using a private key instead of a password. In other words it allows you to use the scp command to connect to a remote host without password.
- -P port: used to specify the port to connect to on the remote host, if different from the default SSH port.
Explaining the -i flag would take a completely separate article so it’s something I will cover outside of this one.
As I said before, the -i flag is used to secure copy files to a remote host without having to provide a password in the terminal.
Let’s move to the -P flag…
Before looking at one example it’s necessary to cover some basics about the SSH protocol.
The default port used by the SSH protocol is port 22.
If this doesn’t make much sense to you, think about a port as a door that gives you access to the target host.
So, considering that the default port for SSH (and SCP) is 22, in all the commands we have seen so far we have connected to port 22 on the target host.
We can confirm that, running the previous scp command and also passing the -v flag that provides verbose output.
At the beginning of the output of the command we will see a line similar to the following:
debug1: Connecting to test_host on port 22. Now, going back to the -P flag…
Occasionally, for security reasons, a remote host might be configured to allow SSH (and SCP) on a different port.
Let’s say the port is 3256, this time the scp command will be:
myuser@localhost:~$ scp -v -P 3256 test_file.txt test_user@test_host:/var/tmp/As a result in the verbose output we will see:
debug1: Connecting to test_host on port 3256. The component configured on the target host that receives connections when we execute the scp o ssh commands, is called SSH server.
Conclusion
That’s it for now, we have covered quite a lot!
You should now have an understanding of the scp command and how it’s used on Linux to perform the secure copy of files and directories.
Finally, it’s time to run some tests on your machine so you can make sure you remember the syntax of the scp command to:
- Copy files from your local machine to a remote host.
- Copy files from a remote host to your local machine.
Very often you might need to transfer multiple files. Instead of transferring them individually it can be handy to transfer an archive that contains the files.
Learn here how to compress files using tar.
See you in the next article 🙂

Claudio Sabato is an IT expert with over 15 years of professional experience in Python programming, Linux Systems Administration, Bash programming, and IT Systems Design. He is a professional certified by the Linux Professional Institute.
With a Master’s degree in Computer Science, he has a strong foundation in Software Engineering and a passion for helping others become Software Engineers.